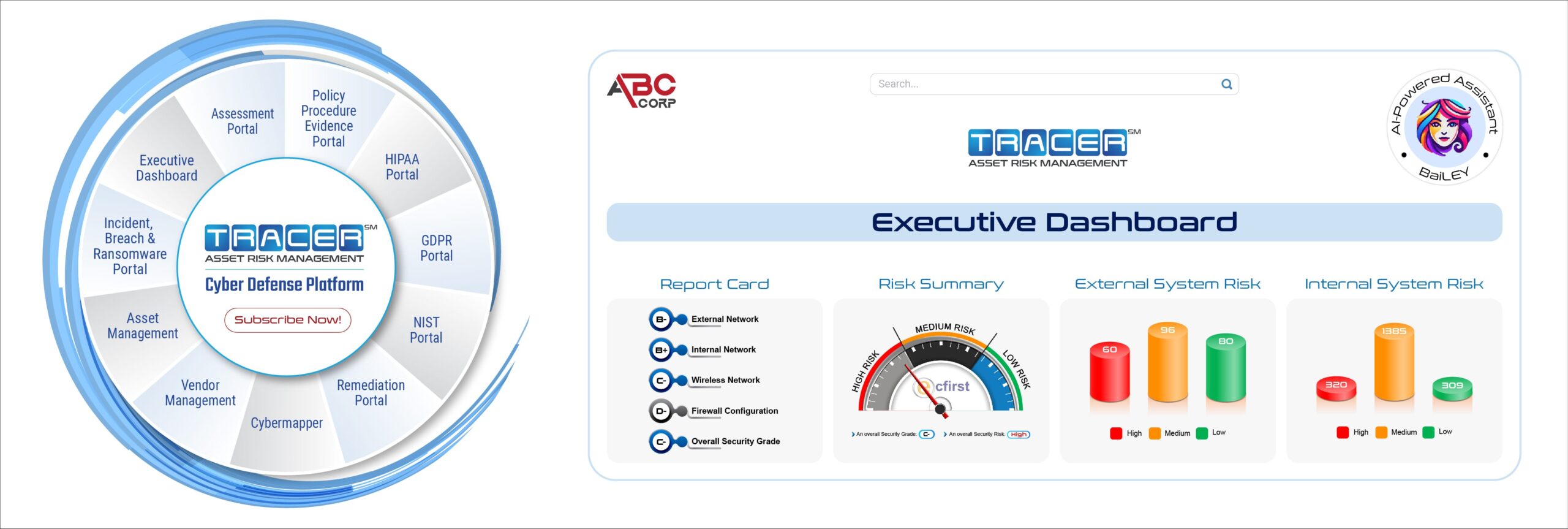
Developed by ecfirst, is software as a service for comprehensive compliance management.
is software as a service for comprehensive compliance management.
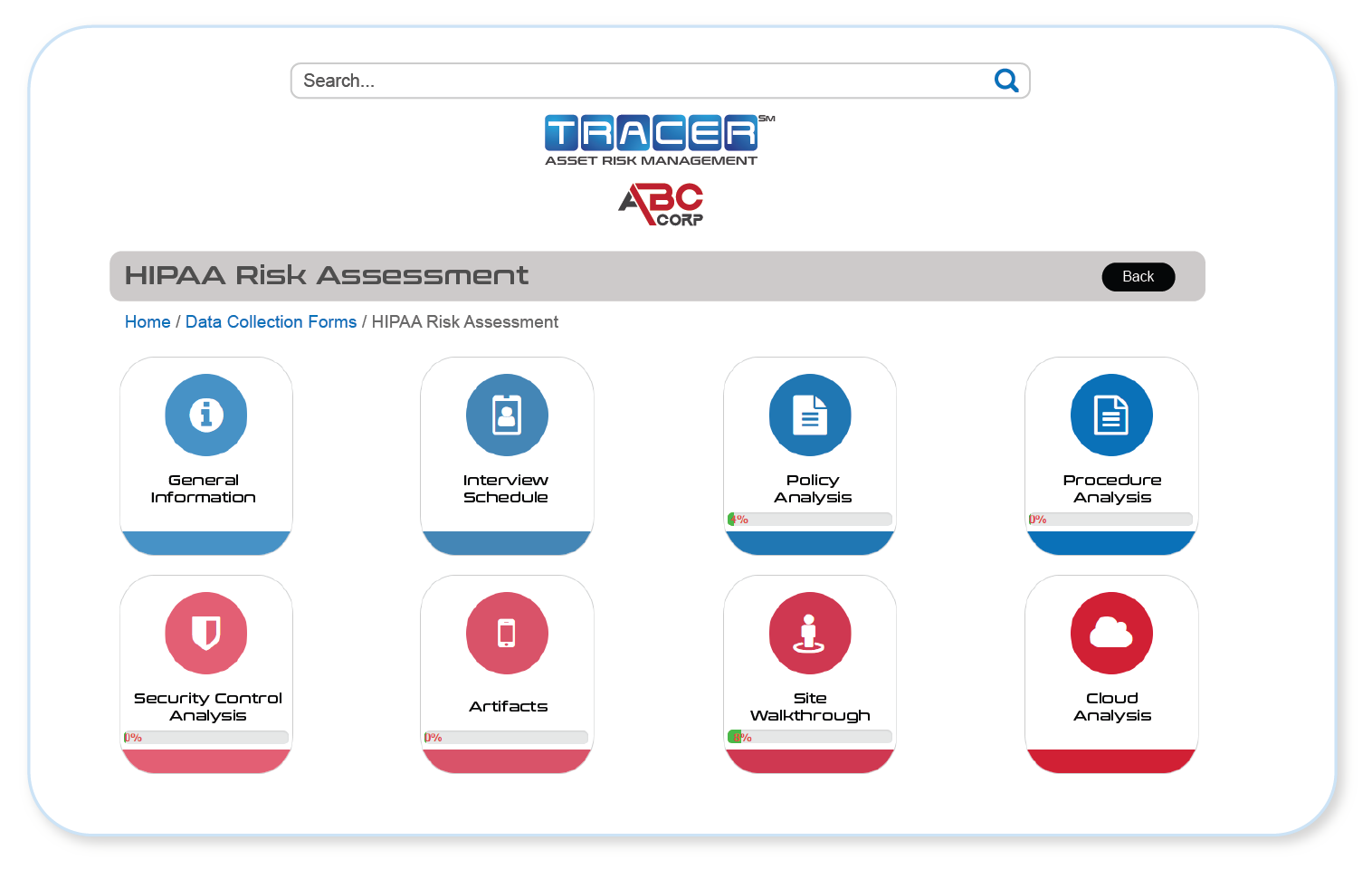
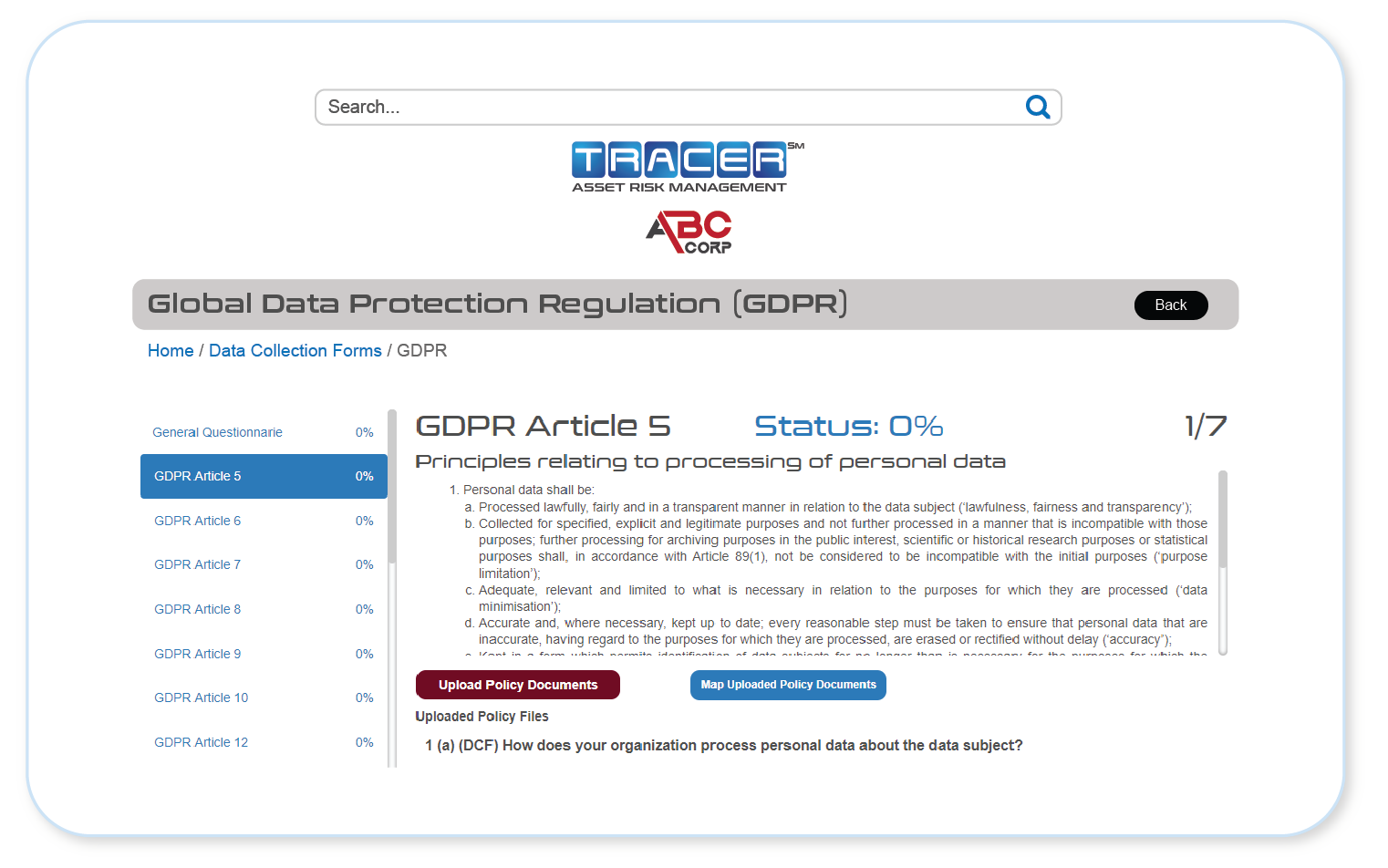
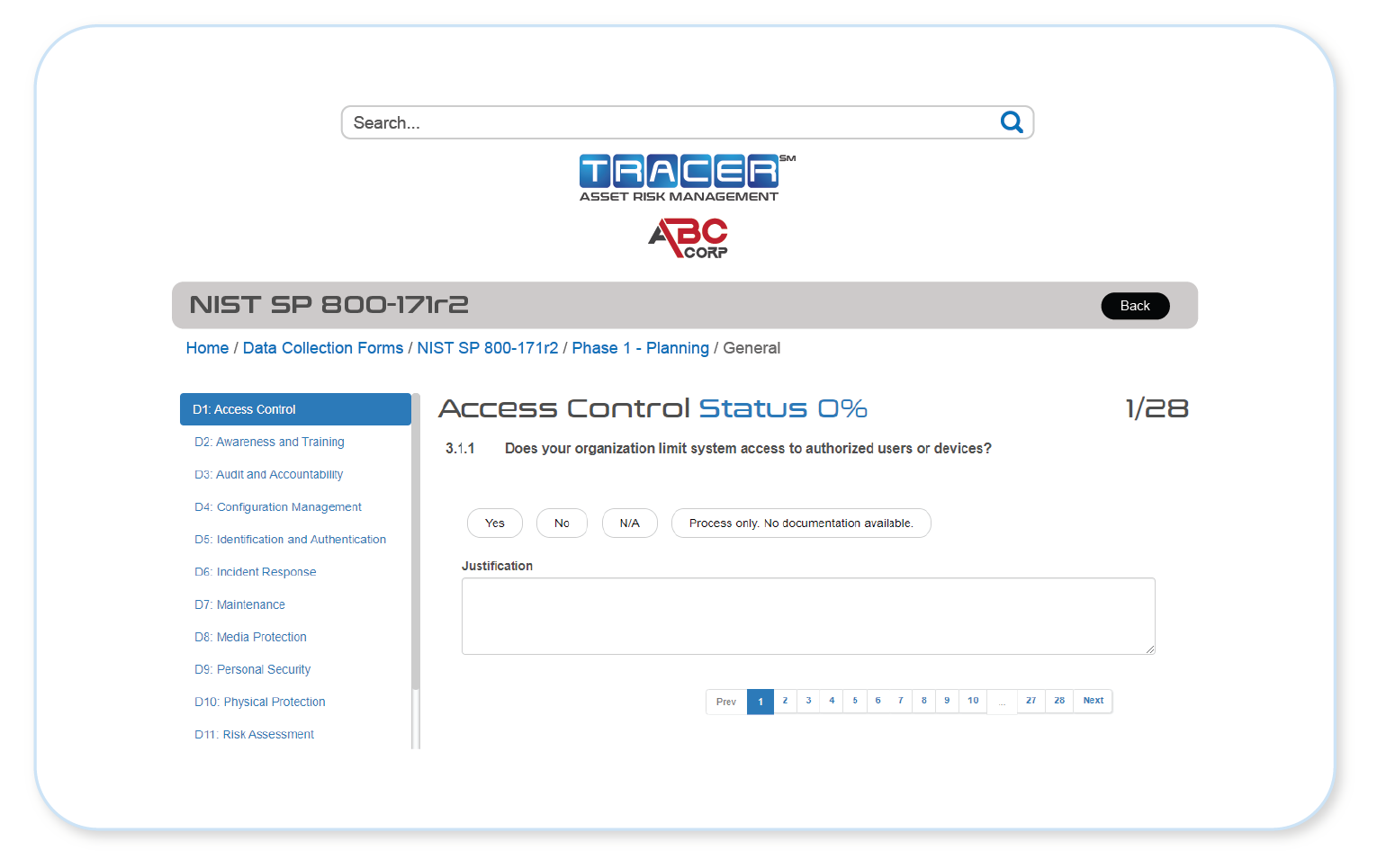
 can assist with management of all core requirements of HIPAA, ISO 27001, NIST Cybersecurity Framework, and many other information security standards, with contents tailored for your organization’s needs.
can assist with management of all core requirements of HIPAA, ISO 27001, NIST Cybersecurity Framework, and many other information security standards, with contents tailored for your organization’s needs.  can also support business continuity processes by aiding in the development of items such as a robust IT Disaster Recovery Plan or thorough Business Impact Analysis.
can also support business continuity processes by aiding in the development of items such as a robust IT Disaster Recovery Plan or thorough Business Impact Analysis.
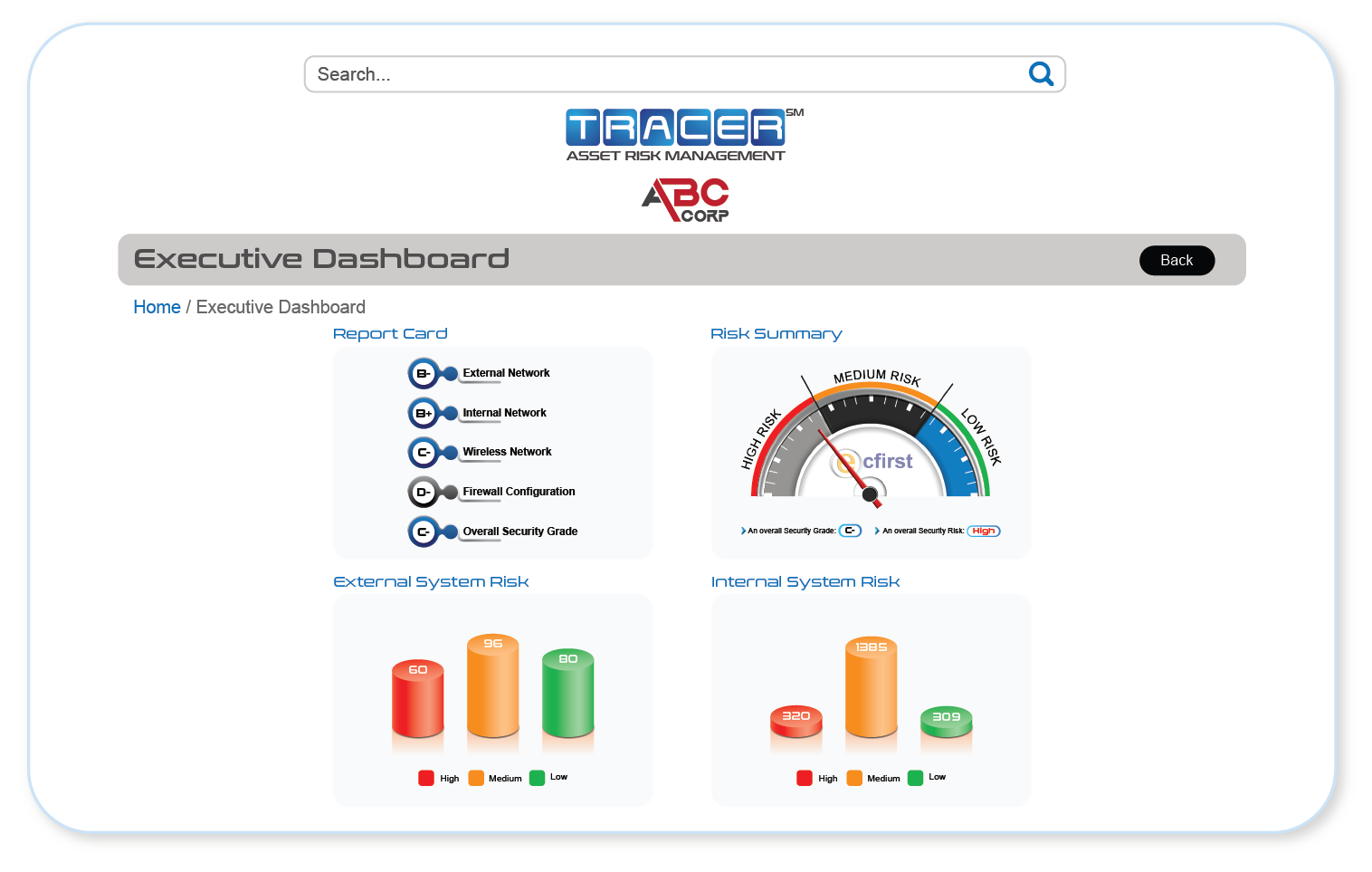
Simple to use, this online portal empowers compliance teams as well as provides executive visibility into compliance management efforts.
 and Data Security
and Data Security
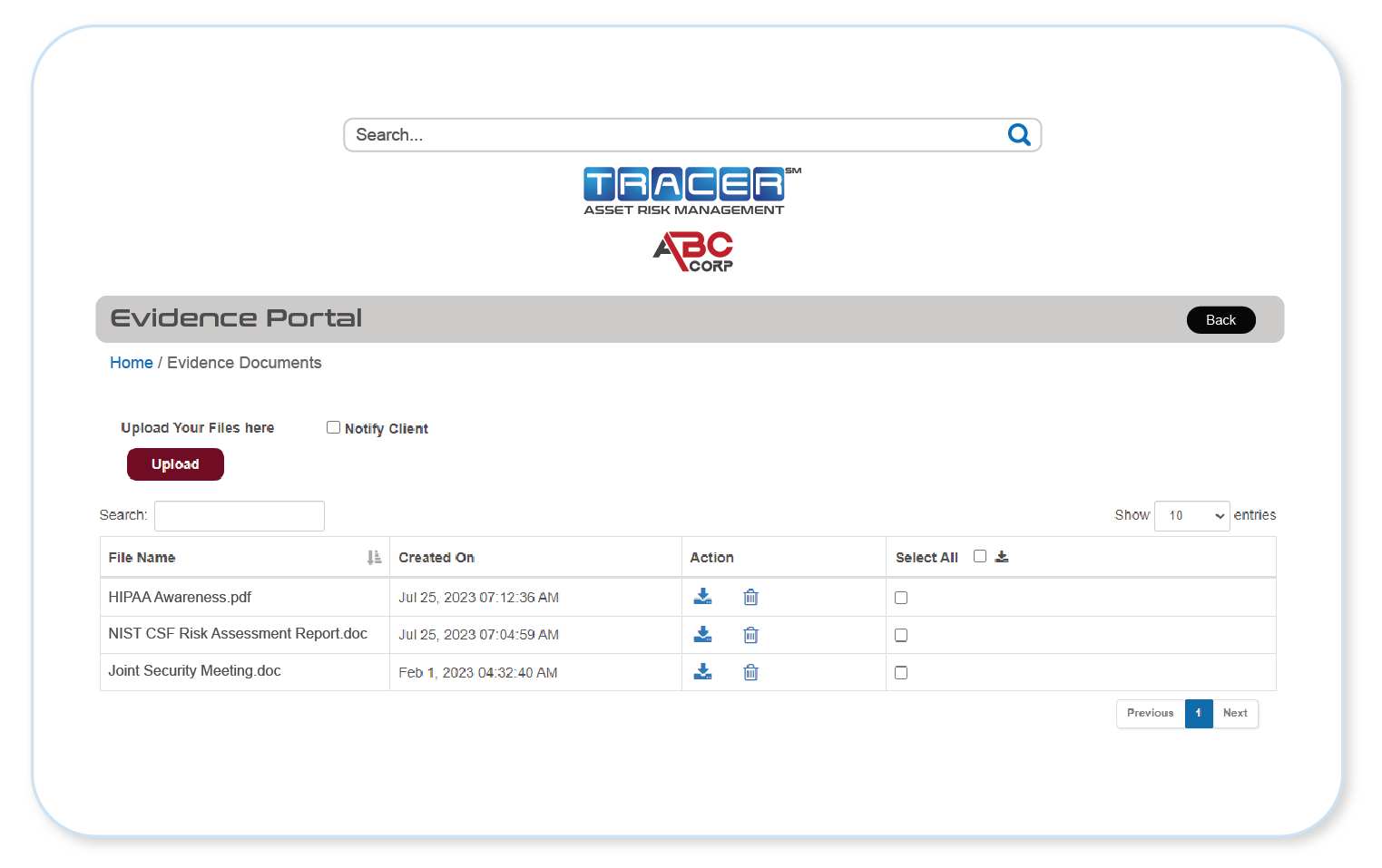
ecfirst takes the protection of data you provide using the  Portal very seriously. All files uploaded to the
Portal very seriously. All files uploaded to the  Portal are encrypted before they are stored in our private access cloud location, separate from the
Portal are encrypted before they are stored in our private access cloud location, separate from the  system itself. ecfirst follows industry best practice for encryption of sensitive data:
system itself. ecfirst follows industry best practice for encryption of sensitive data:
- Industry standard advanced encryption algorithm AES-256-GCM
- Automatic annual encryption key rotation
- Limited restricted access to encryption keys
- Limited restricted access to encrypted data
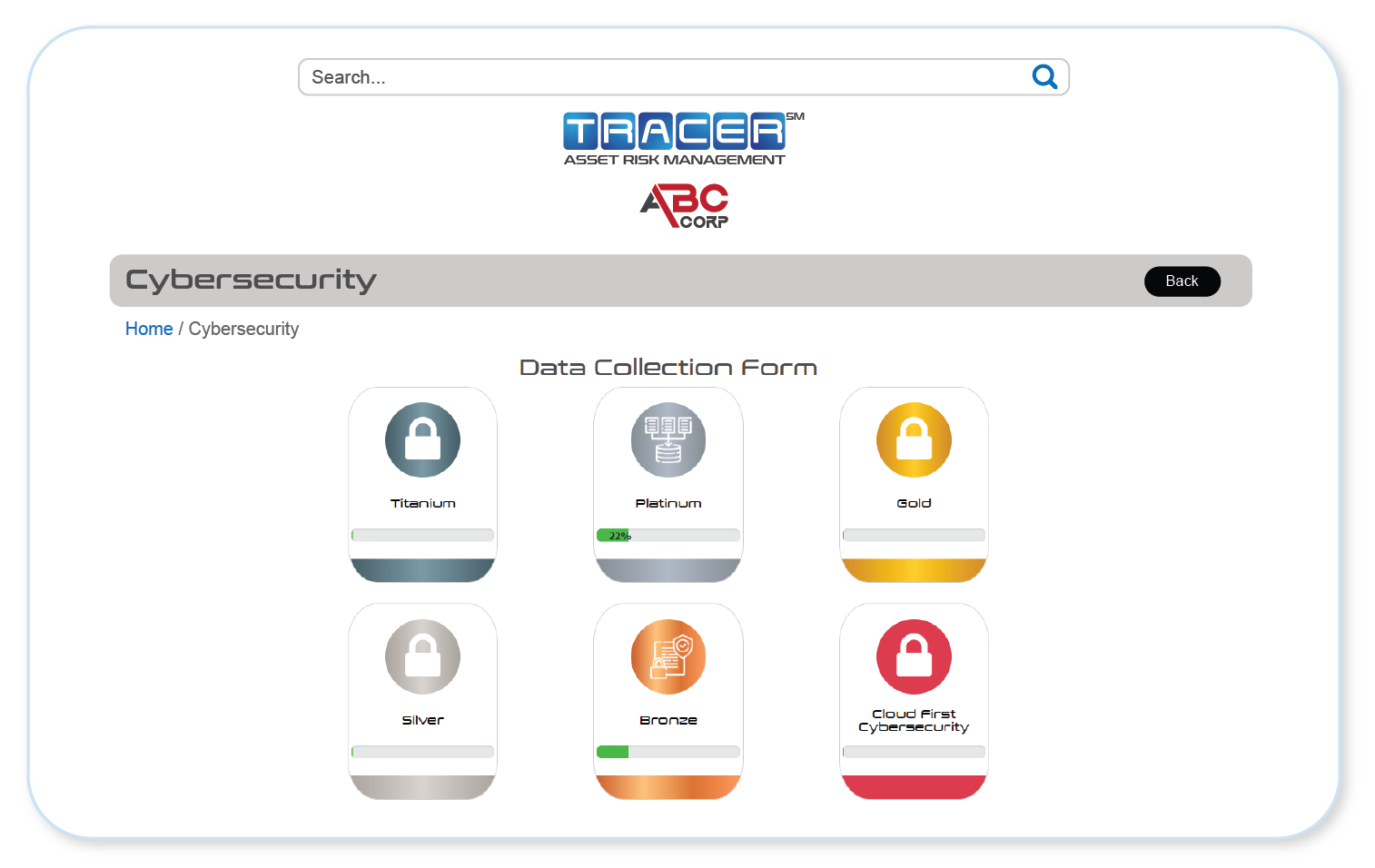
Assessment Portal

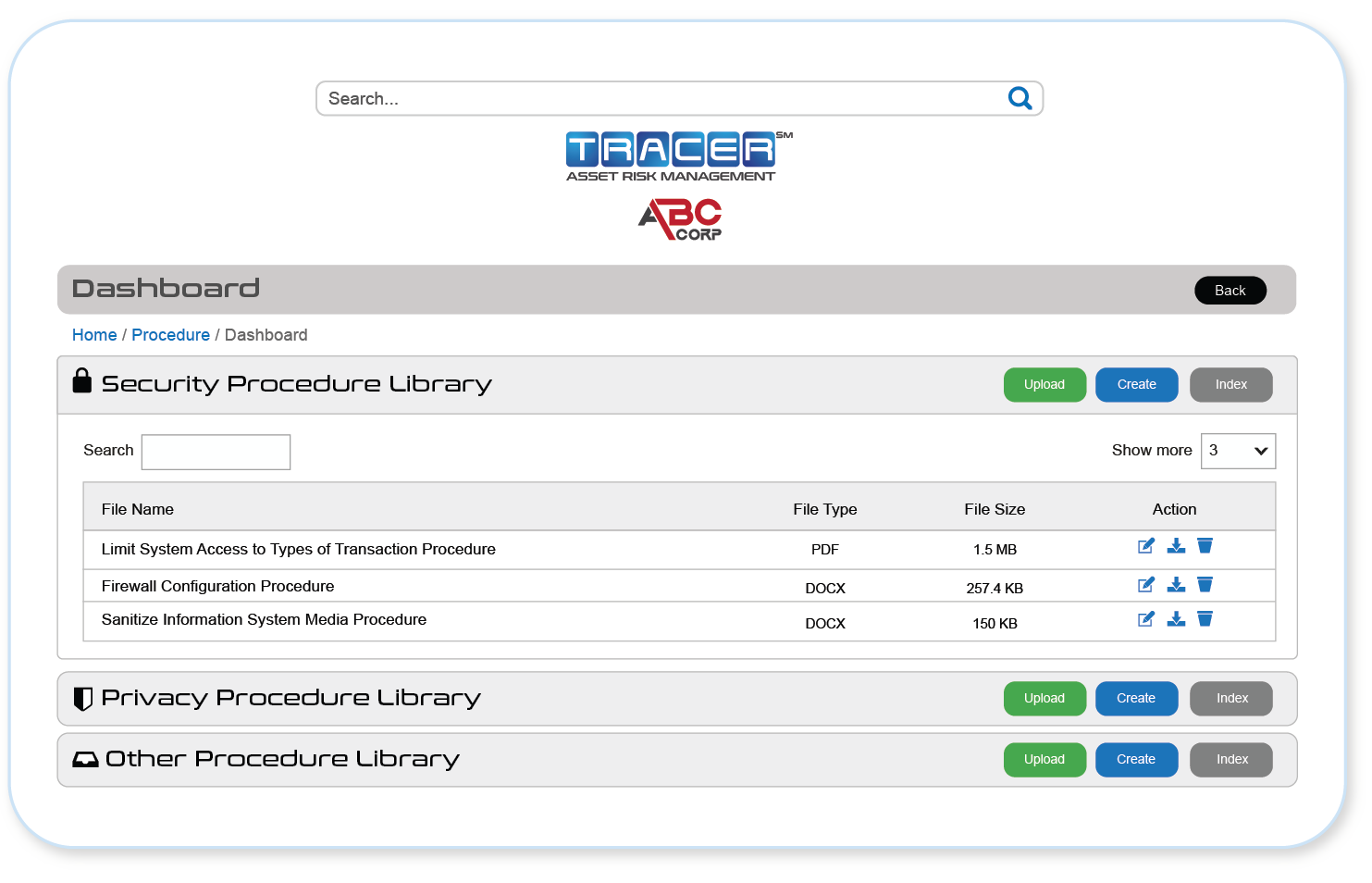
Policy Portal
Organize your compliance and cybersecurity policies and procedures centrally on  . Easily update policies and procedures, as required, to meet compliance mandates and timeframes.
. Easily update policies and procedures, as required, to meet compliance mandates and timeframes.





NIST Cybersecurity Framework Portal





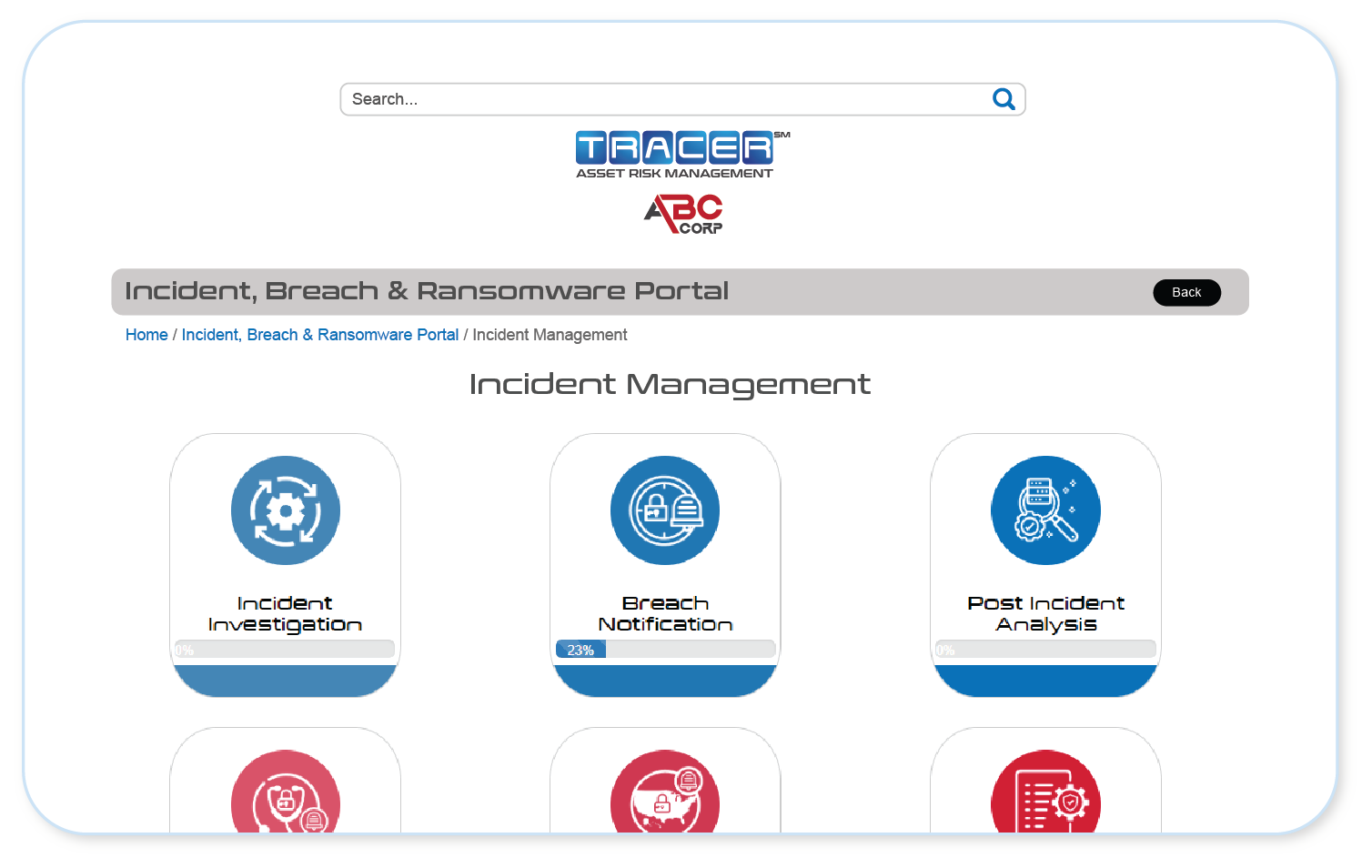
Incident, Breach & Ransomware Portal

Compliance Programs
Due to its variety in coverage, allows management and maintenance of compliance documentation regardless of the information security framework, standards, or regulations your organization is subject to.
Request a Proposal
Readiness Portal
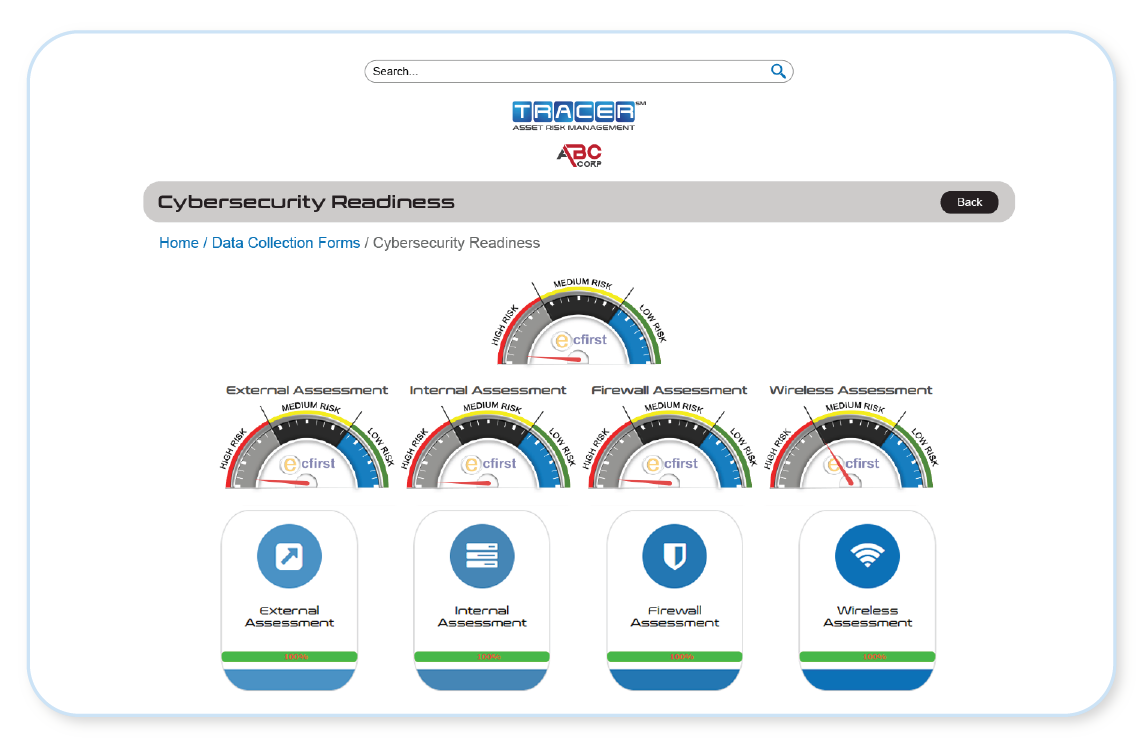
The Readiness Portal within  provides organizations, whether just beginning a Self-Assessment or completing Validation and Certification, a step-by-step path toward their goal.
provides organizations, whether just beginning a Self-Assessment or completing Validation and Certification, a step-by-step path toward their goal.
Contingency Planning
Manage your organization’s contingency planning documentation in  to ensure readiness for unexpected occurrences and swift recovery to standard business operations.
to ensure readiness for unexpected occurrences and swift recovery to standard business operations.