About ecfirst online learning
ecfirst online learning provides access to a library of introductory and advanced courses and modules on compliance regulations and information security.

HIPAA Courses Supported

- Introduction to HIPAA
- HIPAA Security Rule
- Transaction & Code Sets
- HIPAA Fines for Lack of Risk Assessment
- Privacy Awareness Training
- Information Security for End Users
- Information Security for IT Staff
- Introduction to Information Security
- Information Security for Managers
- HIPAA & Security Training for Physicians
- HIPAA Compliance for IT Professionals
- HIPAA & Security for Senior Executives
- HIPAA & Security Training for Clinical Staff
CHA™ & CHP

- Overview – What’s In It For Me? (WIIFM)
- HIPAA / HITECH Act / Final Rule overview
- Privacy Rule

- Overview – What’s In It For Me? (WIIFM)
- HIPAA / HITECH Act/ Final Rule Overview
- Privacy Rule
- Transactions, Code Sets & Identifiers
- Security Rule

CSCS™
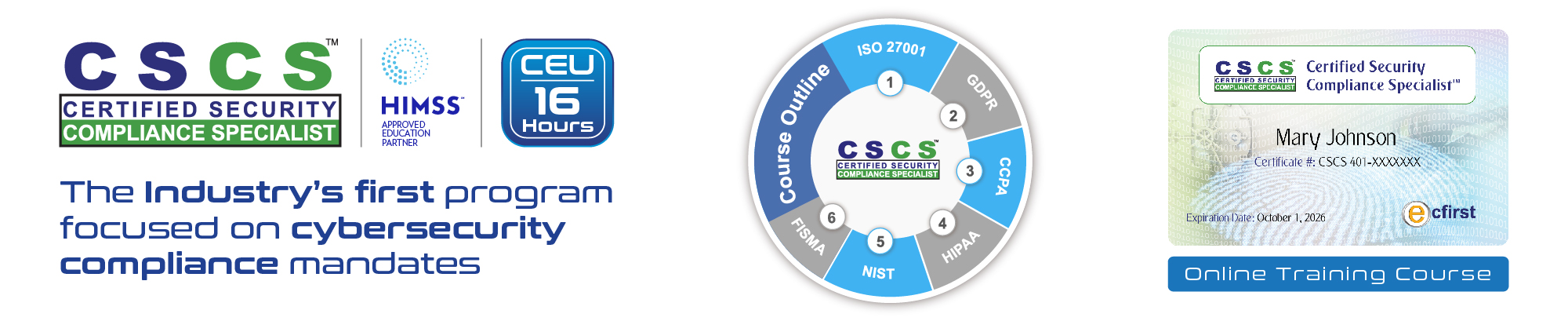
- State of Cybersecurity
- Regulations: Getting Started
- GDPR
- ISO/IEC 27K Series
- Healthcare Information Security
- Payment Card Industry (PCI) Data Security Standard (DSS)
- U.S. State Regulations
- U.S. Federal Regulations
- NIST Frameworks & Guidance
- Study 1: Risk Analysis
- Study 2: Business Impact Analysis (BIA)
- Study 3: Cybersecurity Policies & Procedures
- Study 4: Cybersecurity Strategy
CCSA℠
- Cybersecurity Framework
- Regulations: Getting Started
- Security Incident Management
- Vulnerability Assessment and Penetration Testing
- Essential Cyber Policies
- Encryption
- Establishing a Cybersecurity Program

Training & Certification

- Step through all major sections of HIPAA Final Rule.
- Examine the HIPAA Privacy and Security Rules; HIPAA Transactions Code Sets and Identifiers.

- Evaluate U.S. state cybersecurity mandates, including California, New York, Texas and others.
- Examine ISO 27001 and NIST standards.
- Recognize key concepts to comply with the European Union (EU) General Data Protection Regulation (GDPR).

- Examine and build practical cybersecurity program.
- Step through core components of an incident response plan.
- Review key policies in the areas of risk assessment, mobile devices, cloud computing, encryption, and more.