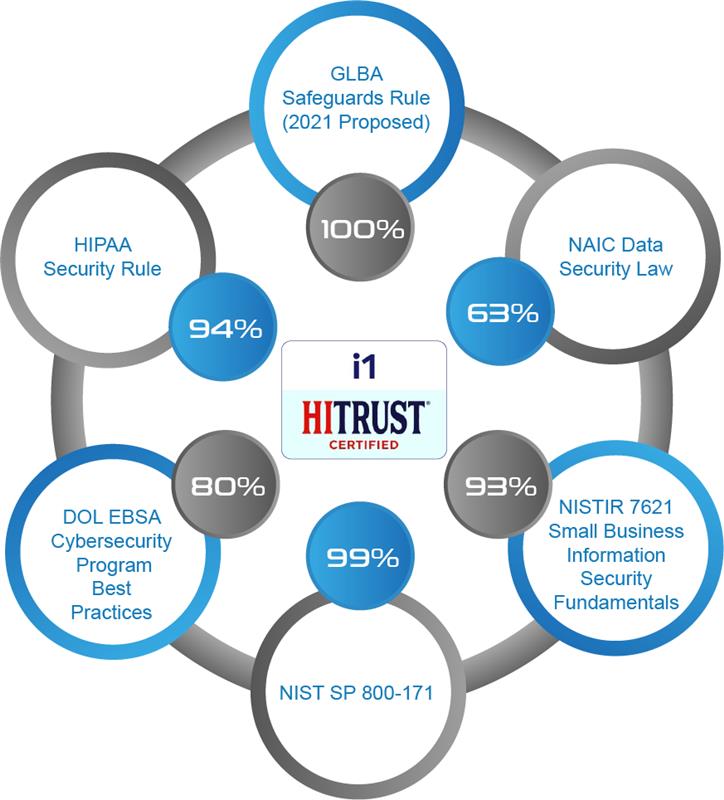
Achieve HITRUST i1 Certification
182 Requirements
HITRUST i1 Facts
| Description | Validated Assessment + Certification |
|---|---|
| Purpose (Use Case) | Provides a moderate level of assurance that addresses cybersecurity leading practices and a broader range of active cyber threats than the e1 assessment |
| Number of HITRUST CSF Requirements on a 2-Year Basis and Maturity Levels Considered | 182 (Year 1), ~60 (Year 2 with Rapid Recertification), Implemented |
| Policy and Procedure Consideration | Minimal |
| Flexibility of Control Selection | No Tailoring |
| Evaluation Approach | 1x5: Implementation control maturity level |
| Level of Effort / Level of Assurance Conveyed | Moderate, (relative to r2 Certification) |
| Control Requirements Performed by Service Providers | Allows Carve-Outs or Inclusion |
| Certifiable Assessment | Yes, 1 Year + Rapid Recertification in Year 2 |
| Supporting Assessments | Readiness, Rapid Recertification |
| Aligned Authoritative Sources | NIST SP 800-171 (Basic and Derived Requirements), HIPAA Security Rule, and HICP for Medium-Sized Organizations |
| Provides Targeted Coverage for One or More Authoritative Sources | No |
| Uses the HITRUST Results Distribution System™ to Share Results | Yes |
| Leverages HITRUST Assurance Intelligence Engine™ (AIE) to Prevent Omissions and Errors | Yes |
| Coverage of Standards and Authoritative Sources | Includes HITRUST Basics, Technically-focused components from GLBA, NAIC, NIST, DOL EBSA, and HIPAA, and the latest Threat Intelligence Data |
| Number of Control Requirement Statements | 182 Static |
| Flexibility of Control Selection | Pre-Set Controls that Leverage Security Best Practices and Threat Intelligence |
| Evaluation Approach | 1x5: Control Implementation Only |
| Level of Effort / Level of Assurance Conveyed | Moderate |
| Certifiable Assessment | Yes, 1-year |
HITRUST AI Cybersecurity

HITRUST AI Cybersecurity for AI ensures organizations mitigate cybersecurity threats, while also addressing privacy, ethics, and transparency risks.
HITRUST AI Risk Management

HITRUST AI Risk Management provides a strong foundation for assessing AI risks, identifying gaps, and drive continuous improvement.